Homomorphic
Encryption
of Commutative Rings
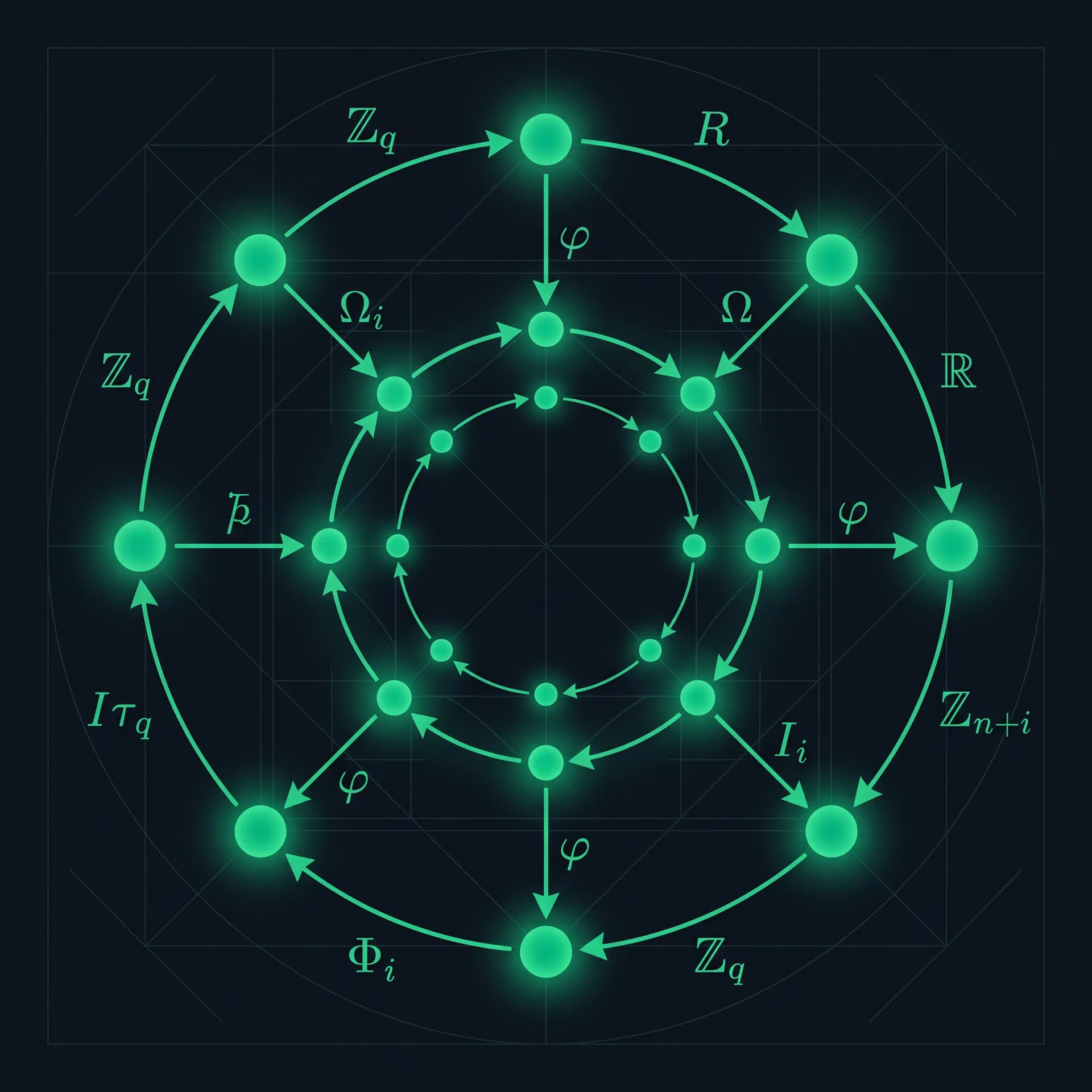
Explore the mathematical foundations of computing on encrypted data — from the algebraic structure of commutative rings to fully homomorphic encryption schemes that preserve ring operations under ciphertext.
Commutative Ring Theory
Homomorphic encryption is fundamentally an algebraic construction. To understand it, we must first understand the ring structures that underpin modern cryptographic schemes.
A ring is a set R equipped with two binary operations — addition (+) and multiplication (·) — satisfying:
- • (R, +) is an abelian group with identity 0
- • (R, ·) is a monoid with identity 1
- • Multiplication distributes over addition
A ring is commutative when for all .
An ideal is a subring that absorbs multiplication: for all and , we have .
The quotient ring consists of cosets with operations inherited from R. This construction is central to building the polynomial rings used in HE.
A map is a ring homomorphism if it preserves both operations:
The kernel is always an ideal of R. By the First Isomorphism Theorem, .
The polynomial ring used in BFV and BGV schemes is:
Here is a power of 2 (e.g., 1024), is a large prime, and elements are polynomials of degree with coefficients in . The relation enables efficient NTT-based multiplication.
The integers with standard addition and multiplication. The prototypical commutative ring.
When splits into linear factors mod a prime , the CRT gives an isomorphism:
This enables SIMD batching — encrypting n values simultaneously and operating on all of them in parallel.
Homomorphic Encryption
A homomorphic encryption scheme allows computation on ciphertexts such that decrypting the result yields the same answer as computing on the plaintexts directly.
The Fundamental Property
An encryption scheme (KeyGen, Enc, Dec, Eval) is homomorphic with respect to a function class if for every :
The evaluation is performed using only the public key — the server never sees the plaintext messages and does not need the secret key .
Types of Homomorphic Encryption
Supports one operation (+ or ×) an unlimited number of times.
Supports both + and × but only for a limited circuit depth before noise overwhelms.
Supports circuits up to a predetermined depth L, set at key generation time.
Supports arbitrary computations of any depth. Achieved via bootstrapping.
The Ring Learning With Errors Problem
The security of BFV and BGV rests on the computational hardness of the Ring Learning With Errors (RLWE) problem, introduced by Lyubashevsky, Peikert, and Regev in 2010.
Given samples where:
with secret and small error , it is computationally hard to distinguish these from uniformly random pairs.
This problem is believed to be hard even for quantum computers, making RLWE-based encryption a leading candidate for post-quantum cryptography. The NIST PQC standardization process selected several RLWE-based schemes.
The original LWE problem operates over vectors in , requiring space for keys. Moving to the ring reduces this to while maintaining comparable security, enabling practical implementations.
Every ciphertext carries a small noise term . Operations grow the noise:
Security level (bits) determines parameter sizes. For 128-bit security: , . Larger allows deeper circuits but increases computation time.
Encryption Schemes
Three major ring-based homomorphic encryption schemes, each with distinct approaches to noise management and plaintext representation.
Scaling-based noise management for integer arithmetic
Uses a scaling factor Δ = ⌊q/t⌋ to embed plaintext in the high-order bits of the ciphertext modulus.
- Homomorphic addition
- Homomorphic multiplication
- Relinearization
- Modulus switching
KeyGen
Secret key is a small binary polynomial. Public key masks it with random a and error e.
| Property | BFV | BGV | CKKS |
|---|---|---|---|
| Plaintext Type | Integers mod t | Integers mod t | Approx. reals |
| Noise Strategy | Scaling (Δ=⌊q/t⌋) | Mod switching | Rescaling |
| Best For | Exact arithmetic | Deep circuits | ML / approx. |
| Bootstrapping | Supported | Supported | Supported |
Interactive Scheme Demos
Walk through live encryption cycles for all three major ring-based HE schemes — BFV for exact integers, BGV with modulus switching, and CKKS for approximate real arithmetic.
Generate a fresh key pair. The secret key s is a small binary polynomial; the public key masks it with random a and error e.
The encryption map Enc: R_t → R_q² is a ring homomorphism with respect to addition. This is the fundamental property that makes homomorphic encryption possible.
Applications & Impact
Homomorphic encryption over commutative rings is transitioning from theoretical curiosity to practical deployment across industries where data privacy is paramount.
Privacy-Preserving Medical Analysis
Hospitals can run diagnostic models on encrypted patient data. The model provider never sees the raw records, and the patient never reveals sensitive health information.
Secure Financial Computation
Banks can compute credit scores, fraud detection, and portfolio analysis on encrypted financial data without exposing individual transaction histories.
Private Machine Learning
Train and run ML models on encrypted data. CKKS enables neural network inference where neither the model weights nor the input data are revealed to the other party.
Verifiable Electronic Voting
Votes are encrypted and tallied homomorphically. The final count can be verified without ever decrypting individual votes, ensuring both privacy and integrity.
Secure Cloud Computing
Outsource computation to untrusted cloud providers. The cloud performs operations on encrypted data and returns encrypted results — the cloud learns nothing.
Genomic Research
Researchers can run genome-wide association studies across encrypted datasets from multiple institutions without sharing raw genomic sequences.
Historical Timeline
Any somewhat homomorphic encryption scheme that can evaluate its own decryption circuit (plus one more NAND gate) can be converted into a fully homomorphic encryption scheme.